Have you heard of RFC 9116? If not, I understand. I don't really know anything by RFC numbering and that is ok. RFC 9116 is a document put out by the Internet Engineering Task Force (IETF) related to vulnerability disclosure. It is important to note that this is not a standard, but for informational purposes only. So what does it do? The focus of this document is on the security.txt file and the format of it. Security.txt is a simple text file that helps an organization describe their … [Read more...] about Security.txt for Vulnerability Disclosure
vulnerability
Is encoding really encoding if it is escaping?
The title might be confusing, let's see if we can clear it up. I saw an article the other day that was giving a comparison between encoding, encryption and hashing. There was a statement made that basically said: Encoding has no security purpose. I thought this was interesting because when training on security topics we mention encoding for specific use cases. For example, when we discuss Cross-Site Scripting, the answer is output encoding. I want to clarify that I agree with the statement … [Read more...] about Is encoding really encoding if it is escaping?
Log4J – Reflection and Progression
Open any social media platform or pull up any mainstream media and undoubtably, you have seen many posts/articles talking about the log4j vulnerability. If you haven't seen this, here is a quick link to catch up https://snyk.io/blog/log4j-rce-log4shell-vulnerability-cve-2021-4428/. This post is not going to be about log4j, nor is it going to go into any of the details the thousands of others articles out there would go through. Instead, I want to discuss this at a higher level. Log4j is just an … [Read more...] about Log4J – Reflection and Progression
What is the difference between Brute Force and Credential Stuffing?
Many people get confused between brute force attacks and credentials stuffing. To help clear this up, here is a simple description of the two. These are both in regards to the login form only. Brute Force Brute force attacks on the login form consist of the attacker having a defined list (called a dictionary) of potential passwords. The attacker will then try each of these defined passwords with each username the attacker is trying to brute force. Put simply, this is a 1 (username) too many … [Read more...] about What is the difference between Brute Force and Credential Stuffing?
Thinking about starting a bug bounty? Do this first.
Application security has become an important topic within our organizations. We have come to understand that the data that we deem sensitive and critical to our business is made available through these applications. With breaches happening all the time, it is critical to take reasonable steps to help protect that data by ensuring that our applications are implementing strong controls. Over the years, testing has been the main avenue for "implementing" security into applications. We have seen a … [Read more...] about Thinking about starting a bug bounty? Do this first.
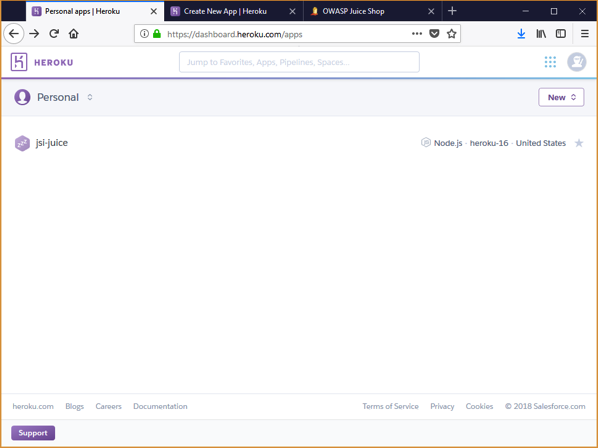
Installing OWASP JuiceShop with Heroku
I am often asked the question by clients and students where people can go to learn hacking techniques for application security. For years, we have had many purposely vulnerable applications available to us. These applications provide a safe environment for us to learn more about hacking applications and the vulnerabilities that are exposed without the legal ramifications. In this post I want to show you how simple it is to install the OWASP Juice Shop application using Heroku. Juice Shop is a … [Read more...] about Installing OWASP JuiceShop with Heroku