Security takes a layered approach to reduce the risk to our organization. Input validation is the perfect example of one of these layers. In most cases, input validation is 1 factor in a multi-pronged approach to protecting against common vulnerabilities. Take any course on secure development and they will, or should, mention input validation as a mitigating control for so many vulnerabilities. You might notice that it always comes with a but. Use input validation, but also use output … [Read more...] about Input validation is less about specific vulnerabilities
applicaiton security
Ep. 102: Intro to Web Security Policies
In this episode James introduces us to the idea of web security policies stored in a security.txt file. We have talked about vulnerability disclosure before and this ties directly into that conversation. Link to Draft: https://tools.ietf.org/html/draft-foudil-securitytxt-03 Link to form to create the file: https://securitytxt.org/ Link to our blog post: https://www.developsec.com/2018/06/26/overview-of-web-security-policies/ For more info go to https://www.developsec.com or follow us on … [Read more...] about Ep. 102: Intro to Web Security Policies
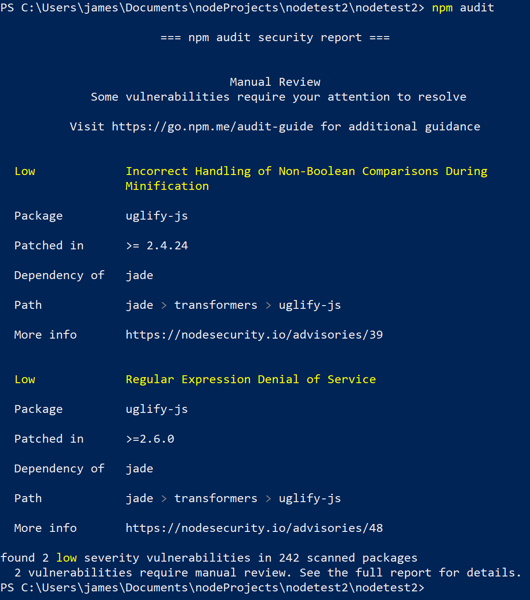
Checking npm packages using npm-audit
Our applications rely more and more on external packages to enable quick deployment and ease of development. While these packages help reduce the code we have to write ourselves, it still may present risk to our application. If you are building Nodejs applications, you are probably using npm to manage your packages. For those that don't know, npm is the node package manager. It is a direct source to quickly include functionality within your application. For example, say you want to hash your … [Read more...] about Checking npm packages using npm-audit
JavaScript in an HREF or SRC Attribute
The anchor (<a>) HTML tag is commonly used to provide a clickable link for a user to navigate to another page. Did you know it is also possible to set the HREF attribute to execute JavaScript. A common technique is to use the onclick event of the anchor tab to execute a JavaScript method when the user clicks the link. However, to stop the browser from actually redirecting the HREF can be set to javascript:void(0);. This cancels the HREF functionality and allows the JavaScript from the … [Read more...] about JavaScript in an HREF or SRC Attribute
Blue Cross Mails USB sticks – Take-Aways
You have information you want to share with your customers, but how do you do it securely? How often have you heard not to click links sent via email? You shouldn't plug in random USB drives to your computer. From a marketing perspective, how do you get large amounts of information, such as videos and specific information, out to your customers? In a report by Fierce Healthcare … [Read more...] about Blue Cross Mails USB sticks – Take-Aways
MongoDBs under attack from ransomware
In recent news, it was identified that MongoDB databases are being exposed on the internet and infected with ransomeware. In a little under a week, the infection count went from 200 to 10,000. That is a quick ramp up. In this case, misconfigurations may bind the database port to the public interface, while also allowing anonymous access. This combination can be devastating. Doing a quick search on Shodan you may find there are thousands of misconfigured MondoDB servers exposed on the … [Read more...] about MongoDBs under attack from ransomware